Adobe released a security hotfix APSB11-29 for ColdFusion 8 and 9 on Tuesday, which fixes two XSS (Cross Site Scripting) vulnerabilities (CVE-2011-2463 and CVE-2011-4368). One vulnerability exists in cfform and the other in RDS.
Our HackMyCF ColdFusion Server Security Scanner has been updated to find the RDS vulnerability remotely (using our free scan). We can't readily detect the cfform vulnerability remotely because of the proper conditions to exploit are not predictable to find (we would have to crawl your entire site to look for the proper conditions).
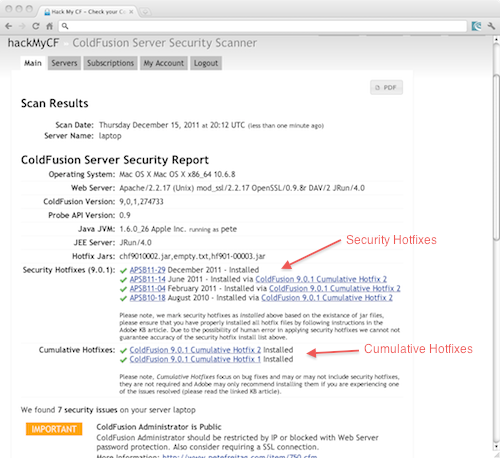
We can however detect it, if you have a HackMyCF Subscription, and have setup the HackMyCF probe (a cfm file you place on your server which allows for encrypted communication). You also get even more detail in your report, showing which Cumulative Hotfixes you have installed, as well as which security hotfixes were applied (currently shows that for 9.0.1 only). Here's a screenshot of what a ColdFusion server security report can look like for a HackMyCF subscriber:
As you can see from the above screenshot we recently added a listing of Cumulative Hotfixes installed, that way its easy to know if you are running Cumulative hotfix 1 or cumulative hotfix 2, etc. You can also see things like the JVM version you are running, etc.
For a limited time you can use coupon code 543m to take $5 off the first 3 months of your subscription.