ColdFusion Server Security Scanner
Updated on November 17, 2023
By Pete Freitag
By Pete Freitag
My company Foundeo Inc. released a new free web service today called HackMyCF that allows you to scan your ColdFusion server to detect the absence of recent ColdFusion security hotfixes as well as other security problems.
The site generates an email report detailing what security issues were found, here's an example:
I would love to hear your feedback!
BTW, we now have a CFML Code Security Scanner called Fixinator!
ColdFusion Server Security Scanner was first published on October 21, 2009.
If you like reading about coldfusion, security, hotfixes, or scanner then you might also like:
- Determining Which Cumulative Hotfixes are Installed on ColdFusion
- You May Need to Reapply CF Security Hotfix CVE-2009-1877
- Fixinator fixes unscoped variables
- ColdFusion searchImplicitScopes and APSB24-14
The Fixinator Code Security Scanner for ColdFusion & CFML is an easy to use security tool that every CF developer can use. It can also easily integrate into CI for automatic scanning on every commit.
Try Fixinator
CFBreak
The weekly newsletter for the CFML Community
Comments
Concerning the "Server Software Disclosure" warning, here's an article that describes how to change the server header in IIS7.
http://blogs.technet.com/stefan_gossner/archive/2008/03/12/iis-7-how-to-send-a-custom-server-http-header.aspx
The comments also contain an interesting discussion of whether this is really necessary from a security standpoint, and some insinuations about why Microsoft didn't make this a simple change.
http://blogs.technet.com/stefan_gossner/archive/2008/03/12/iis-7-how-to-send-a-custom-server-http-header.aspx
The comments also contain an interesting discussion of whether this is really necessary from a security standpoint, and some insinuations about why Microsoft didn't make this a simple change.
by David Hammond on 10/22/2009 at 10:04:15 AM UTC
Darn it, I meant to say concerning the "Server Header Version Disclosure" warning. The "Server Software Disclosure" is a simple change in IIS.
by David Hammond on 10/22/2009 at 10:08:42 AM UTC
@Gary - The FCKeditor vulnerability is an important one, it is installed as part of ColdFusion 8, and is located under /CFIDE/ See http://www.petefreitag.com/item/704.cfm for more info.
by Pete Freitag on 10/22/2009 at 10:09:09 AM UTC
@Mark thanks!
@steveeray would you mind emailing me your server domain so I can look into it. Is it possible that some files still existed in your CFIDE after the update.
@David great link, thanks!
@steveeray would you mind emailing me your server domain so I can look into it. Is it possible that some files still existed in your CFIDE after the update.
@David great link, thanks!
by Pete Freitag on 10/22/2009 at 10:12:14 AM UTC
@David, it looks like that latest version of Microsoft URLScan supports IIS 7 / Windows 2008: http://www.iis.net/extensions/UrlScan
by Pete Freitag on 10/22/2009 at 10:53:30 AM UTC
I love this. Great idea! I never knew I needed to apply an Apache patch.
Unfortunately I have some other servers I would like to check but I do not have an E-mail address at those domains since our work E-mails are all on a secondary domain that the site doesn't operate on. Is there a way I can check those?
Unfortunately I have some other servers I would like to check but I do not have an E-mail address at those domains since our work E-mails are all on a secondary domain that the site doesn't operate on. Is there a way I can check those?
by Brad Wood on 10/22/2009 at 4:34:16 PM UTC
@Brad, yes I added a feature that allows you to use any email address provided that you can create a temporary file in the web root using a certain file name. Just enter the domain and email and it will tell you how to do it.
by Pete Freitag on 10/22/2009 at 5:06:17 PM UTC
Hi Pete-
I ran HackMyCf before I applied any security patches on my 8.01 server yet it found nothing. Could it be because I have CFAdmin behind a firewall or an alternate port.
I ran HackMyCf before I applied any security patches on my 8.01 server yet it found nothing. Could it be because I have CFAdmin behind a firewall or an alternate port.
by doug on 02/15/2010 at 2:23:33 PM UTC
Doug - yes if it can't find /CFIDE then it really limits what it can find. But that is a good thing!
by Pete Freitag on 02/15/2010 at 2:51:37 PM UTC
Does that mean I do not need to apply these patches since I have secured CFIDE. We have always moved them to an alternate port and left that without public access. Only someone on our VPN can see it which is extremely limited.
I have a second question as well. In our PCI Compliance we found we were open to XSS attacks on our forms. One of the developers wrote something that escapes <>" and "" and the example code the compliance company sent no longer works.
I know this is a stretch to answer but if we prevent those characters could that be the end of the PCI Compliance certification issue. IT seems too easy.
I have a second question as well. In our PCI Compliance we found we were open to XSS attacks on our forms. One of the developers wrote something that escapes <>" and "" and the example code the compliance company sent no longer works.
I know this is a stretch to answer but if we prevent those characters could that be the end of the PCI Compliance certification issue. IT seems too easy.
by Doug on 02/15/2010 at 5:12:07 PM UTC
@Doug: No need to write you own functions. Use the HTMLEditFormat() function to make a string safe to include in HTML, and use the jsStringFormat() function to make a string safe for JavaScript.
Properly escaping ALL user-controlled strings on your site is neccessary to prevent XSS.
Properly escaping ALL user-controlled strings on your site is neccessary to prevent XSS.
by Brad Wood on 02/16/2010 at 12:00:13 AM UTC
@Doug - I would still recommend applying the patches even if our remote tool can't find them it doesn't mean a hacker can't.
As for the XSS, you really need to remove more than just <>"' to be protected in all cases and HTMLEditFormat doesn't totally do the trick, for example HTMLEditFormat doesn't escape single quotes.
To be free of XSS concerns you need to strip out <>'"();#
As for the XSS, you really need to remove more than just <>"' to be protected in all cases and HTMLEditFormat doesn't totally do the trick, for example HTMLEditFormat doesn't escape single quotes.
To be free of XSS concerns you need to strip out <>'"();#
by Pete Freitag on 02/16/2010 at 11:14:56 AM UTC
 Pete Freitag
Pete Freitag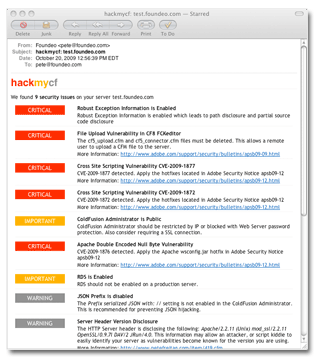
Thanks for putting in the time and effort to make it publicly available.